Pack Contributors:
- Paul-Adrian Dragoi
Contributions are welcome and appreciated. For more info, visit our Contribution Guide.
Manage Secrets and Protect Sensitive Data through HashiCorp Vault. Ingest and normalize Vault Audit logs.
Contributions are welcome and appreciated. For more info, visit our Contribution Guide.
In addition to the HasiCorp Vault Integration for managing secrets and credentials on HashiCorp Vault, this pack includes Cortex Data Modeling (XDM) Rules and Parsing Rules for ingesting and normalizing HashiCorp Vault Audit Logs.
Follow the steps below to configure ingestion of Hashicorp Vault audit logs into Cortex XSIAM.
Run the audit enable command from the Vault server CLI for enabling a File audit device to write JSON audit log records to a file. For example:
vault audit enable file file_path=/var/log/vault_audit.logSee also:
Install the HashiCorp Vault content pack from Cortex XSIAM Marketplace.
Configure an XDR Collector:
Create an XDR Collector installation package as described here.
Install the XDR Collector created installation package on the HashiCorp Vault server:
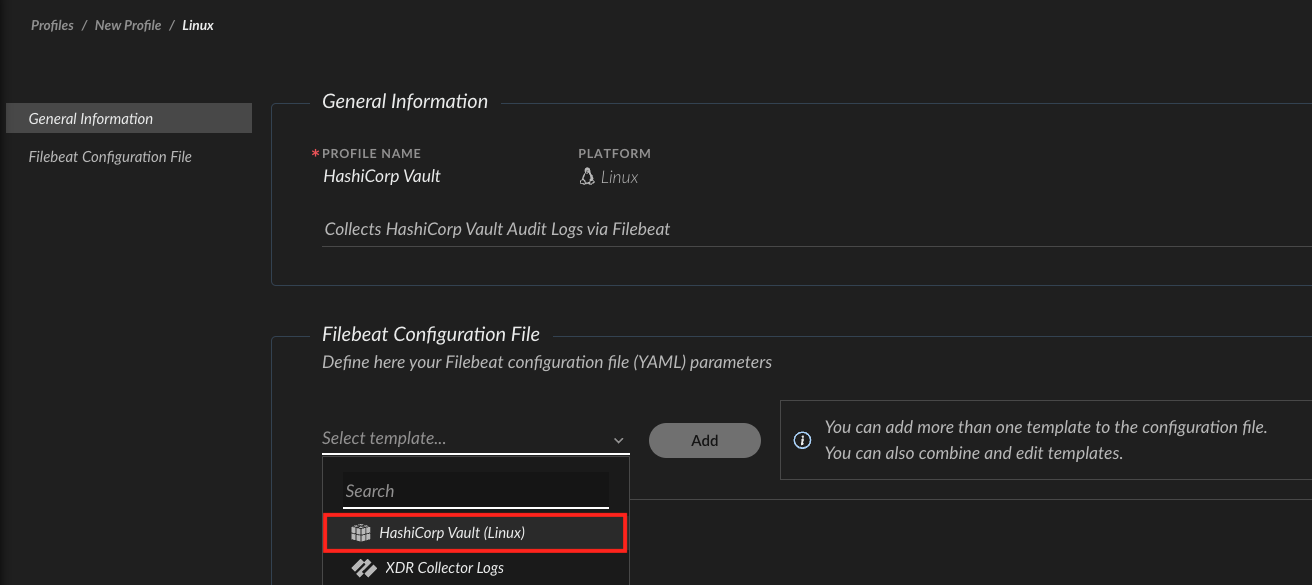
Configure an XDR Collector Filebeat profile:
filebeat.inputs:
- type: filestream
enabled: true
id: hashicorp-vault
paths:
- /var/log/vault_audit.log # customize path as needed
processors:
- add_fields:
fields:
vendor: hashicorp
product: vaultApply the configured Filebeat profile to the target HashiCorp Vault server by attaching it to a policy as described on Apply profiles to collection machine policies.
After the Cortex XSIAM Collector starts ingesting logs from the configured path on the HashiCorp Vault server, you could query the collected audit logs under the hashicorp_vault_raw dataset.
datamodel dataset = hashicorp_vault_raw | fields hashicorp_vault_raw._raw_log, _time, xdm.event.id, xdm.event.type, xdm.event.original_event_type, xdm.event.operation_sub_type, xdm.event.outcome, xdm.event.outcome_reason, xdm.source.ipv4, xdm.source.host.ipv4_public_addresses, xdm.source.port, xdm.auth.auth_method, xdm.source.user.identifier, xdm.source.user.groups, xdm.target.resource.id, xdm.target.resource.name, xdm.target.resource.type, xdm.target.resource.sub_type, xdm.target.user.identifier, xdm.target.user.username, xdm.network.rule, xdm.network.session_id, xdm.observer.versionContributions are welcome and appreciated. For more info, visit our Contribution Guide.
| Name | Description |
|---|---|
| HashiCorp Vault | Manage Secrets and Protect Sensitive Data through HashiCorp Vault. |
| Name | Description |
|---|---|
| HashiCorp Vault | Manage Secrets and Protect Sensitive Data through HashiCorp Vault. |
| Name | Description |
|---|---|
HashiCorp Vault Modeling Rule |
| Name | Description |
|---|---|
HashiCorp Vault Parsing Rule |
| Name | Description |
|---|---|
HashiCorp Vault (Windows) | |
HashiCorp Vault (Linux) |
| Pack Name | Pack By |
|---|---|
| Base | By: Cortex XSOAR |
| Pack Name | Pack By |
|---|
| Pack Name | Pack By |
|---|---|
| Aggregated Scripts | By: Cortex XSOAR |
| Base | By: Cortex XSOAR |
Added Data Modeling Rules for normalizing HashiCorp Vault Audit Logs which are ingested into the hashicorp_vault_raw dataset (Available from Cortex XSIAM 2.3). You can now query ingested audit logs over the normalized XDM schema. For example:
datamodel dataset = hashicorp_vault_raw | fields hashicorp_vault_raw._raw_log, _time, xdm.event.id, xdm.event.type, xdm.event.original_event_type, xdm.event.operation_sub_type, xdm.event.outcome, xdm.event.outcome_reason, xdm.source.ipv4, xdm.source.host.ipv4_public_addresses, xdm.source.port, xdm.auth.auth_method, xdm.source.user.identifier, xdm.source.user.groups, xdm.target.resource.id, xdm.target.resource.name, xdm.target.resource.type, xdm.target.resource.sub_type, xdm.target.user.identifier, xdm.target.user.username, xdm.network.rule, xdm.network.session_id, xdm.observer.versionAdded Parsing Rules for ingesting Hashicorp Vault Audit Logs into the hashicorp_vault_raw dataset and populating the system _time field with the raw audit log time field timestamp value (Available from Cortex XSIAM 2.3).
New: Added an XDR Collector Filebeat profile template for ingesting audit logs from a HashiCorp Vault Linux server via a file audit device (Available from Cortex XSIAM 2.3).
New: Added an XDR Collector Filebeat profile template for ingesting audit logs from a HashiCorp Vault Windows server via a file audit device (Available from Cortex XSIAM 2.3).
| Certification | Certified | Read more |
| Supported By | Cortex | |
| Created | November 9, 2020 | |
| Last Release | April 27, 2026 |
